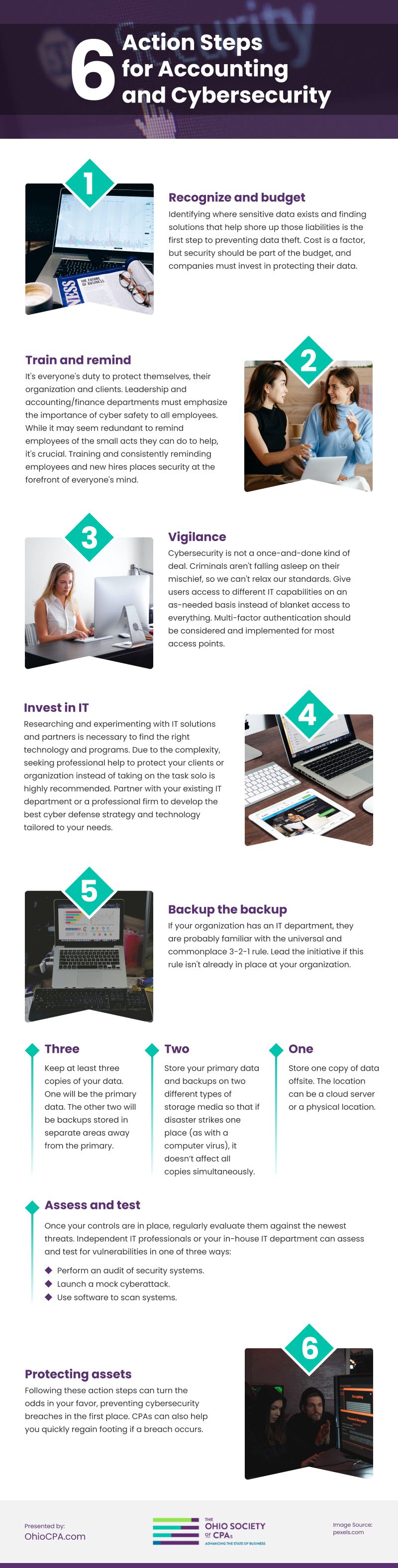
Accounting and Cybersecurity: Six Action Steps
 (cottonbro / pexels)
(cottonbro / pexels)
Cyberattacks are progressively complicated and costly. According to a 2020 FBI cybercrime analysis, $1.8 billion was lost due to business email compromises alone.
With the emergence of hybrid remote work environments, cybersecurity risks are becoming more common and difficult to mitigate. So-called “bad actors” have more entry points with our increased use of Wi-Fi and digital platforms.
Hoping for the best is not a solid game plan when money and peace of mind are at stake. Accounting and finance professionals play a pivotal role in their organization’s and client’s security. At the very least, infiltrations affect a company’s reputation. At worst, people’s identities, savings and retirement funds are in jeopardy.
Learn how you can help protect your clients and your organization. The six action steps below will better prepare you for increasingly common threats.
Recognize and budget
The first step in fixing any problem is admitting there is a problem, right? No matter how secure you think your data is, cybercriminals constantly develop clever ploys to steal it. Security loopholes and new technology allow these criminals to access data and money in new ways.
First, identify where sensitive data exists, like email chains, vendors, partners and third parties. Once you’ve located existing high-priority risks and potential compromises, find solutions that help shore up those liabilities.
Identifying loopholes within your company and finding a product or service to make you more secure takes time and capital. Keep in mind that this expense is necessary for today’s technological age, and security should be part of the budget.
Train and remind
Leadership and accounting/finance departments must emphasize the importance of cyber safety to all employees and new hires. While it may seem redundant to remind employees of the small acts they can do to help (not clicking on unknown or untrustworthy links, verifying before divulging), it’s crucial.
Training and consistently reminding employees and new hires places security at the forefront of everyone’s mind and fosters a culture of conscientiousness and ownership. It’s everyone’s duty to protect themselves, their organization and clients.
Vigilance
Cybersecurity is not a once-and-done kind of deal. Criminals aren’t falling asleep on their mischief, so we can’t relax our standards.
We must assume that someone is attempting to extract critical data from us right now and all the time. Once that mentality catches on, it’s easier to promote and implement a zero-trust policy around the office concerning IT matters.
Consider giving users access to different IT capabilities on an as-needed basis instead of blanket access to everything. Multi-factor authentication should be considered and implemented for most access points, primarily as more employees work remotely on less secure servers.
An excellent offensive strategy is to establish protection controls along with detection methods. Include a defensive system for how you can anticipate attacks on crucial data, resist those attacks and recover what’s lost. A solid plan will improve your resiliency and get you back on track should a cyberattack occur.
Invest in IT
Due to the complexity, seeking professional help to protect your clients or organization instead of taking on the task solo is highly recommended.
Researching and experimenting with IT solutions and partners is necessary to find the right technology and programs. Partner with your existing IT department or a professional firm to develop the best cyber defense strategy and technology tailored to your needs.
How does one start to find the right fit? It’s essential to ask good questions to find the best partner or services. You’ll want to know how they can improve existing risks. Ask them to train you and other employees to avoid becoming a target and teach you to use any new software.
Backup the backup
If your organization has an IT department, they are probably familiar with the universal and commonplace 3-2-1 rule. Lead the initiative if this rule isn't already in place at your organization.
Three–Keep at least three copies of your data. One will be the primary data. The other two will be backups stored in separate areas away from the primary.
Two–Store your primary data and backups on two different types of storage media so that if disaster strikes one place (as with a computer virus), it doesn’t affect all copies simultaneously.
One–Store one copy of data offsite. The location can be a cloud server or a physical location.
Assess and test
Once your controls are in place, regularly evaluate them against the newest threats. Independent IT professionals or your in-house IT department can assess and test for vulnerabilities in one of three ways:
- Perform an audit of security systems.
- Launch a mock cyberattack.
- Use software to scan systems.
Protecting assets
CPAs possess the necessary insights to help protect their organization and clients against cybersecurity threats. Following these six action steps can turn the odds in your favor, preventing cybersecurity breaches in the first place and helping you quickly regain your footing if a breach does occur.
The Ohio Society of CPAs (OSCPA) will be covering more about cybersecurity at our Mega Tax Conference. Join our Society for this and many more quality CPE learning opportunities that will make you a better CPA, tax or financial professional and make for a more secure economy for the entire state. Check out our website to learn more.
Infographic
The hybrid remote work environments are making the already complicated and costly cybersecurity risks more common and difficult to mitigate. What should you do to protect the organization and its clients? Money and peace of mind are at stake. Moving fast and putting up a solid game plan is a must. Learn how accounting and finance professionals can handle this situation. Read on.